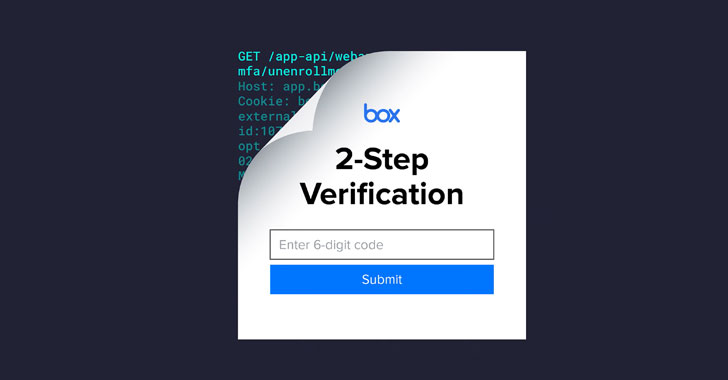
Thus, when a Box user who is enrolled for SMS verification logs in with a valid username and password, the service sets a session cookie and redirects the user to a page where the TOTP can be entered to gain access to the account.
"Box misses that the victim hasn't enrolled [in] an authenticator app, and instead blindly accepts a valid authentication passcode from a totally different account without first checking that it belonged to the user that was logging in," the researchers said.